1,560 SingPass user accounts breached
SINGAPORE — More than 1,500 SingPass accounts have been cracked, possibly exposing these users’ sensitive personal information, such as where they live and how much they earn.
SINGAPORE — More than 1,500 SingPass accounts have been cracked, possibly exposing these users’ sensitive personal information, such as where they live and how much they earn.
Although no losses have been reported so far and there is no evidence at this point to suggest that SingPass’ system has been compromised, about one-quarter, or 419, of these users have had their passwords illegally reset, said the Infocomm Development Authority of Singapore (IDA) yesterday.
SingPass was set up for Singapore residents — aged 15 and above — in 2003 to perform more than 340 online transactions with government agencies. Examples of these transactions include accessing Central Provident Fund accounts, filing income taxes and checking medical records. There are now more than 3.3 million SingPass users.
The breach surfaced over the weekend when 11 SingPass users raised the alarm after receiving letters informing them that they had requested for a password reset, though they had not.
After SingPass operator CrimsonLogic flagged the problem on Monday evening, the IDA launched a probe and learnt the scale of the breach: A total of 1,560 SingPass users have had their account profiles illicitly updated to be tied to a disproportionately small pool of Singapore-registered mobile numbers. The IDA declined to say how many of these suspicious mobile numbers there were.
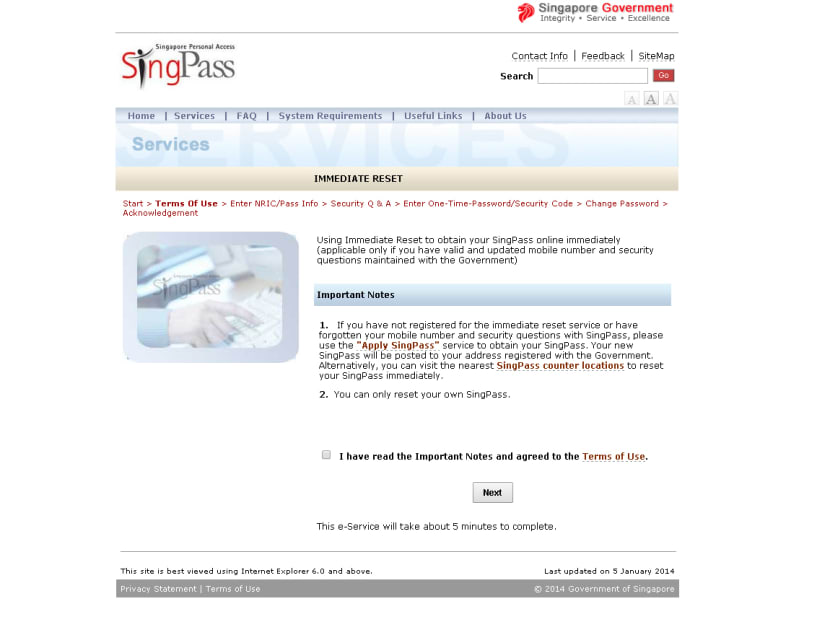
A one-time password is sent to a user’s listed mobile number as an added layer of security check when he or she wants to change his or her SingPass password. Further, the user also has to answer at least two out of a list of questions, for verification.
In a hastily-convened press conference yesterday evening, the IDA said it lodged a police report on Tuesday. The SingPass passwords of all of those affected have also been reset and users are in the process of being notified.
The latest breach comes in the wake of several cases of confidential private data being stolen. For instance, in December last year, Standard Chartered said bank statements of 647 of its private banking clients had been stolen from a server of a printing company.
A month earlier, the data of about 4,000 individuals — including their names, email addresses, phone numbers and, in some cases, nationalities — that was stored on the Singapore Art Museum’s (SAM) website was exposed on an overseas website earlier that month.
IT security experts told TODAY the breach could have been due to SingPass data being stolen from some online database, or through leaks exploited by malware infecting users’ computers.
Mr Anthony Lim, who is a member of the Application Security Advisory Board at not-for-profit association for information security professionals ISC2, said data containing SingPass account information could have been inadvertently leaked or found by the perpetrators.
Mr Chong Rong Hwa, staff malware researcher from network security firm FireEye, said: “The attackers could then guess the passwords if the user did not use a strong password.” He pointed out that users could have also infected their computers unknowingly by visiting websites with malicious bugs. The software would then be able to capture data from the users’ computers, including NRIC or personal information they had previously keyed in.
While the experts agreed that users have a part to play by changing their passwords regularly, Mr Chong suggested that security for the SingPass system be beefed up by installing a mechanism that sends out alerts when a hitherto infrequent SingPass user’s account sees a spike in activity, for instance.
A two-factor authentication system — a standard feature for e-banking — could also be considered, though Mr Chong pointed out challenges such as the cost of issuing all users with a security token, as well as having to revamp the system.
Currently, users only need to key in their NRIC and SingPass password.
Ms Jacqueline Poh, IDA managing director, said: “We continue to explore the use of two-factor authentication for e-government transactions, particularly for those involving sensitive data ... In the meantime, we have put in place multiple levels of security such as captcha and sending letters to your residential addresses when SingPass passwords have been changed. These measures are already in our system.”
She stressed that this incident underlines the importance of taking personal responsibility for cybersecurity. “The Government strongly urges all SingPass users to take the necessary precautions to enhance their cybersecurity ... Users should also install anti-virus software and update all their software regularly,” she added.