Hackers stole data of PM Lee and 1.5 million patients in 'major cyberattack' on SingHealth
SINGAPORE — An unprecedented cyber-attack on Singapore's largest healthcare group SingHealth saw the personal and data of 1.5 million patients stolen, including that of Prime Minister Lee Hsien Loong.
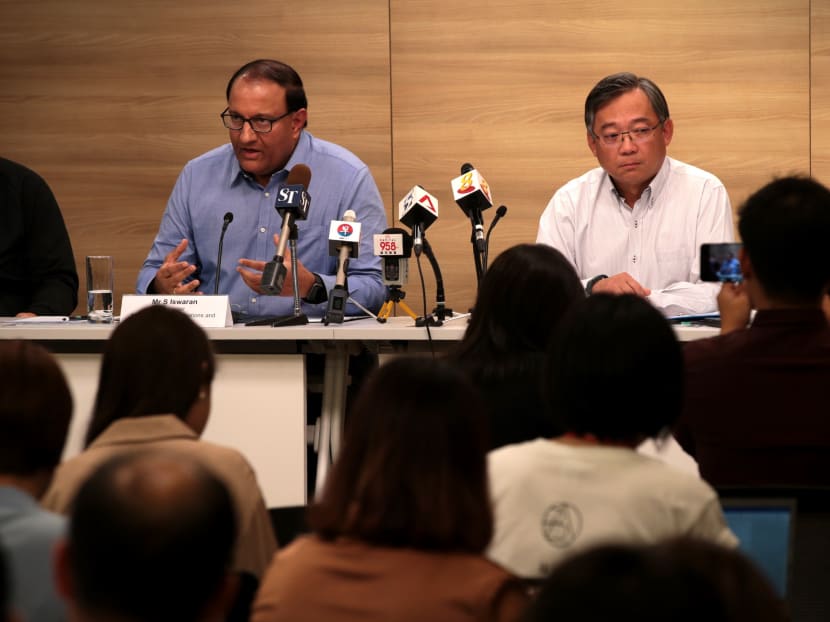
Mr S Iswaran, Communications and Information Minister, attends a press conference alongside Health Minister Gan Kim Yong on SingHealth's cyber attack.
SINGAPORE — An unprecedented cyber-attack on Singapore's largest healthcare group SingHealth saw the personal data of 1.5 million patients stolen, including that of Prime Minister Lee Hsien Loong.
The authorities disclosed on Friday (July 20) that hackers broke into SingHealth's IT systems and repeatedly targeted to steal PM Lee's data and records of medication given to him.The week-long attack, which was carried out between June 27 and July 4, could be a state-sponsored effort, some cyber-security experts told TODAY. While the authorities did not name any suspects, they repeatedly stressed that the attack was not the work of casual hackers or criminal gangs.
The experts declined to speculate on the source of the attack but noted that few entities have the capability to mount such attacks. Media reports and studies in recent years have pointed to China, North Korea, Russia and the United States as among the countries with the resources to mount such sophisticated online attacks.
The breach of SingHealth's systems also saw hackers illegally access and copy the non-medical personal particulars of 1.5 million patients. Around 160,000 of them who had received outpatient treatments also had their medication records stolen, with PM Lee and several government ministers among this group.
The authorities did not reveal the identities of the other government leaders affected.
At a press conference on Friday, Mr David Koh, chief executive of the Cyber Security Agency (CSA) of Singapore, said that the authorities are in touch with and co-operating with its security partners — both here and overseas — as they grapple with what led to the attack.
Mr S Iswaran, Communications and Information Minister, said at the press conference that the Government will tap all its relevant resources and alliances, whether "domestic or if necessary international", to get to the bottom of the matter.
Apologising for the cyber breach, Health Minister Gan Kim Yong noted that the public healthcare sector sees its role as "not just providing good patient care, but also safeguarding the confidentiality of patients' data".
"I am deeply sorry that this has happened… I would like to apologise (to) the affected patients."
The hackers stole personal records such as the names, national registration identification card numbers, addresses, genders, race and dates of birth of 1.5 million patients who visited SingHealth's specialist outpatient clinics and polyclinics from May 1, 2015 to July 4 this year.
The affected institutions included the Singapore General Hospital, Changi General Hospital, KK Women's and Children's Hospital, the National Heart Centre Singapore, the Singapore National Eye Centre, and the National Cancer Centre Singapore.
Mr Lee, whose personal particulars and outpatient medication records were stolen, was "specifically and repeatedly targeted", the authorities said.
Asked why his records were targeted, Mr Koh from CSA would only say that "it's perhaps best not to speculate what the attackers had in mind".
Mr Koh also said that there was "no evidence" the information has been used in any other transaction, put on sale or made available online.
Mr Lee, who has fought off cancer twice, was given a clean bill of health after he took ill abruptly during the National Day Rally in August 2016. In May 2015, Mr Lee was given the all-clear for prostate cancer after undergoing surgery in February that year to remove his cancerous prostate gland. He had a previous brush with cancer in 1992, when he suffered from intermediate-grade malignant lymphoma.
Police investigations into the cyber-attack, which the authorities described as "deliberate, targeted and well-planned", are ongoing.
As for the stolen patient records, the authorities assured the public that they had not been tampered with.
"No other patient records, such as diagnoses, test results or doctors' notes, were breached. We have not found evidence of a similar breach in other public healthcare IT systems," the Ministry of Health (MOH) and Ministry of Communications and Information (MCI) said in a press statement.
STATE-SPONSORED ATTACKS?
There have been mounting concerns in recent years over the proliferation of state-sponsored cyber-attacks aimed at both multinationals and governments.
In the aftermath of this serious cyber breach, some cyber-security experts are saying that it could be a state-sponsored effort. Medication data of patients, they said, could be financially lucrative for hackers, and when it comes to government leaders, their stolen data could be used for malicious political ends.
On how SingHealth's IT system was breached, the CSA's investigations found that it was through a "front-end workstation", and hackers later obtained log-in details to access the database.
Database administrators at the Integrated Health Information Systems, the technology agency for the public-healthcare sector, did not detect signs of unusual activity until July 4.
On discovering the intrusion, the agency's investigators "acted immediately to halt the activity... while putting in place additional cyber-security precautions," the MOH and MCI said.
Six days later, on July 10, the investigators confirmed that SingHealth's systems had been hit by a cyber-attack, that data was stolen from June 27 to July 4. They then informed the relevant parties. On July 12, SingHealth lodged a police report.
The hackers did not stop their activities as monitoring efforts were stepped up, but they did not manage to steal more data after July 4.
The MOH and MCI said that all patient records in SingHealth's IT system remain intact, healthcare services were not disrupted during the attack, and patient care was not compromised.
COMMITTEE OF INQUIRY TO BE SET UP
Asked if the breach could be the result of a human lapse and if any disciplinary action was being taken, Mr Gan said that this was "an important issue", but his ministry's focus for the moment was to reach out to the affected patients and ensure the IT systems are robust.
Mr Iswaran, who is also the Minister-in-charge of Cyber Security, will convene a Committee of Inquiry (COI), chaired by retired Senior District Judge Richard Magnus, to look into the matter and recommend measures to better secure public-sector IT systems against similar attacks.
Mr Gan said that the Government would be able to decide on the actions to be taken once the COI's reports are out. "It's too early to establish the facts (and it's) better to leave it to the COI to carry out the investigation."
As for whether the COI will be conducted in public, Mr Iswaran said that there may be a combination of private and public hearings, though he will leave it to the committee to judge which aspects would be suited to a public or private setting.
He explained that some areas may be subject to operational security considerations, and the interests of the country and Singaporeans "may not be best served" if these were aired in public.
Other aspects of the committee's work that are in the public interest and devoid of operational security considerations are likely to be done in public, he added.
ROLL-OUT OF NEW SYSTEMS SUSPENDED
As part of the follow-up to the cyber attack, the Smart Nation and Digital Government Group completed a scan of all government systems and found no evidence of compromise.
The authorities, however, are suspending the roll-out of new information and communications technology systems while they carry out a security review.
Asked about the Smart Nation projects that have been put on hold, Mr Iswaran said that the business of government cannot come to a standstill on account of the cyber-attack.
Breaches of this scale are not uncommon, he added. The United States National Security Agency and Britain's National Health Service also experienced similar attacks.
"These occurrences of cyber-security breaches happen even in some of the most secure systems around the world. So, I think we've to keep the incident in perspective and then allow due process to take its course," Mr Iswaran said.
He added that new systems are being held off as an exercise in prudence, to review the safety measures and put in place extra safeguards where necessary — it "does not mean that we bring everything to a halt".
"As of now, there's no assessment that any particular project (is) going to be materially affected," he said.
"We cannot let us set this back on our smart nation initiative because that is the way of the future. That is the way to ensure… efficient public services, competitive economy and the kind of opportunities we're trying to talk about for Singaporeans. We cannot go back to (the days of) pen and paper… It will severely impair our efficiency and productivity."
Emeritus Senior Minister Goh Chok Tong, who said in a Facebook post that his "non-medical personal particulars with SingHealth had been stolen", also said that Singapore "cannot stop the digital advance and must strive to build the most secure smart nation".
REVIEW OF PUBLIC HEALTHCARE IT PROJECTS
On the healthcare front, the National Electronic Health Record (NEHR) system, in place since 2011, is set to require mandatory data submission, under a new Healthcare Services Bill expected to be enacted in Parliament later this year. For instance, a typical general practitioner's clinic will be asked to share information such as its patients' demographics, number of visits, diagnoses and allergies.
Mr Gan said that this process would "have to take a pause" for a while, so that the authorities can look into the cyber-security measures for the system in order to strengthen it further before moving ahead. The existing NEHR system, for which security measures are in place, will continue.
Other public healthcare IT projects will also be reviewed, and programmes involving personal information will take a longer time than others with lower cyber-security risk.
Mr Gan said that, ultimately, the focus right now should be to strengthen the systems and beef up cyber security.
"We cannot assume that the threat has disappeared and we must continue to be vigilant (and) monitor our Internet activities, so that we can detect them early if there are indeed further intrusions. We must not let our guards down."